Becoming quantum-ready: the challenges
Quantum computing is poised to disrupt much more than technology. The legal and regulatory landscape are likely to be impacted
Quantum computing is poised to disrupt much more than technology. The legal and regulatory landscape are likely to be impacted

Artificial intelligence has already reshaped industries, workflows, and daily life. Yet, what we see today is still an early stage
Cryptography is often presented as unbreakable. When implemented correctly, that’s true. However, history shows a record of cryptography failures that
AI is no longer confined to research labs or sci-fi scenarios. It is embedded in our daily lives, influencing how

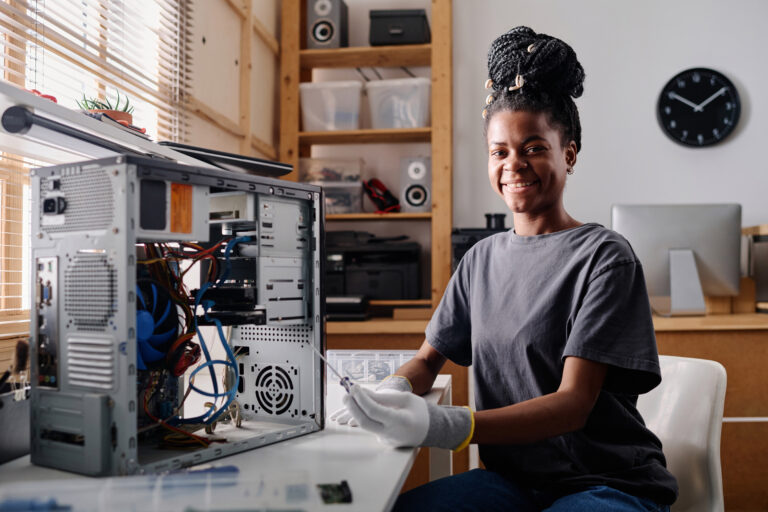
The story of hacking is often told as a tale of lone male geniuses in dark rooms, fingers flying over

If machine learning is the engine behind artificial intelligence, then data is the fuel. No matter how advanced an algorithm

For most of modern history, trust in financial systems has been mediated by institutions. Banks verify transactions, governments issue currency,

Hacking today is both art and science, balancing technical skill with strategy, threat analysis, and real-world consequences. While popular culture

Cryptography has a reputation for strength. Properly designed algorithms, backed by rigorous mathematics, can withstand immense computational effort. In theory,




Articles you can enjoy without specific knowledge
Start learning new topics from their basic concepts
Get into the nitty-gritty of things with advanced topics
Crack your knuckles and get ready on your terminal