
Women who shaped vulnerability disclosure
In the early days of hacking, discovering a vulnerability often meant choosing between two risky options: keep the discovery secret,

In the early days of hacking, discovering a vulnerability often meant choosing between two risky options: keep the discovery secret,

For more than two decades, the cybersecurity community has relied on a shared language to identify security flaws in software

From the BBS Underground to the Bundestag, Germany’s Chaos Computer Club Became the World’s Most Respected Hacker Collective. In the

From dancing baby GIFs in the ’90s to absurdist TikTok trends and politically weaponized memes, meme culture has evolved into

How many times have you seen the ISO 27001 badge on an IT company website? Of course, you might intuitively
Imagine downloading a patch to update a critical system, and that patch contained the malware to hack you. That really

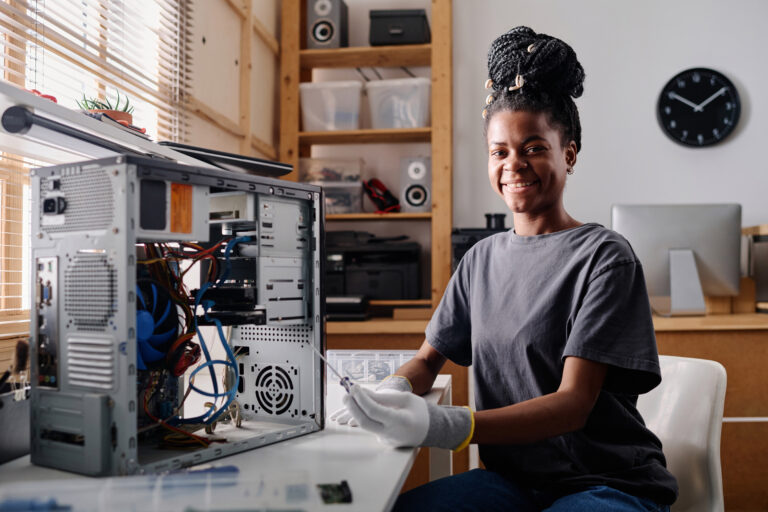
Many people entering the cybersecurity field believe that the only way to demonstrate their skills to a prospective employer is

Have you ever wondered what the most destructive malware is? In January 2003, a computer worm became the fastest-spreading worm




Articles you can enjoy without specific knowledge
Start learning new topics from their basic concepts
Get into the nitty-gritty of things with advanced topics
Crack your knuckles and get ready on your terminal