
Postel, Crocker, and RFC
Who decides what protocols and technologies are used on the Internet? Who enforces the standards and the infrastructure required to

Who decides what protocols and technologies are used on the Internet? Who enforces the standards and the infrastructure required to

When people say a machine “learns,” they are not describing understanding in a human sense. Instead, they are referring to

One of the most critical challenges of the early Internet was how to organize and identify the growing number of

Scams often appear random. An unexpected message, a suspicious email, a connection request from a stranger. But behind most of

When most people hear the word “cryptography,” they picture spies, secret codes, or government intelligence operations. In reality, cryptography is

When the World Wide Web first appeared, publishing online still required technical expertise. Creating a website involved writing HTML by
For decades, the security of modern cryptography has depended on the difficulty of mathematical problems. Factoring large numbers secures RSA.
Before the web, before social media, and even before most people had access to the Internet, there were bulletin board

Scams rarely follow a single script. What appears to be an isolated fraud attempt is usually part of a broader




Articles you can enjoy without specific knowledge
Start learning new topics from their basic concepts
Get into the nitty-gritty of things with advanced topics
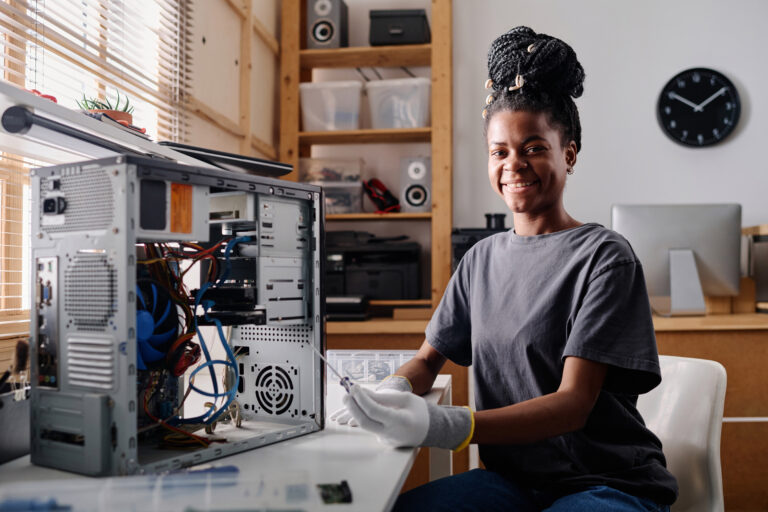
Crack your knuckles and get ready on your terminal