
Automating identity governance
Identity governance used to be a manual spreadsheet activity that most teams dreaded. Cloud environments changed those expectations. Administrators can

Identity governance used to be a manual spreadsheet activity that most teams dreaded. Cloud environments changed those expectations. Administrators can

Today, open source spans every continent and underpins most of the world’s online infrastructure. What began as a small academic

Cryptocurrency investing can feel like stepping into another world: full of unfamiliar terms, price swings, and endless opportunities. Yet, with
Cybersecurity relies on a wide range of cognitive skills. Threat hunting, OSINT investigation, incident response, red team operations, and policy

After years of wait, Stranger Things’s Season 5 – the closing chapter of the Hawkins’ saga – is arriving on

From the BBS Underground to the Bundestag, Germany’s Chaos Computer Club Became the World’s Most Respected Hacker Collective. In the

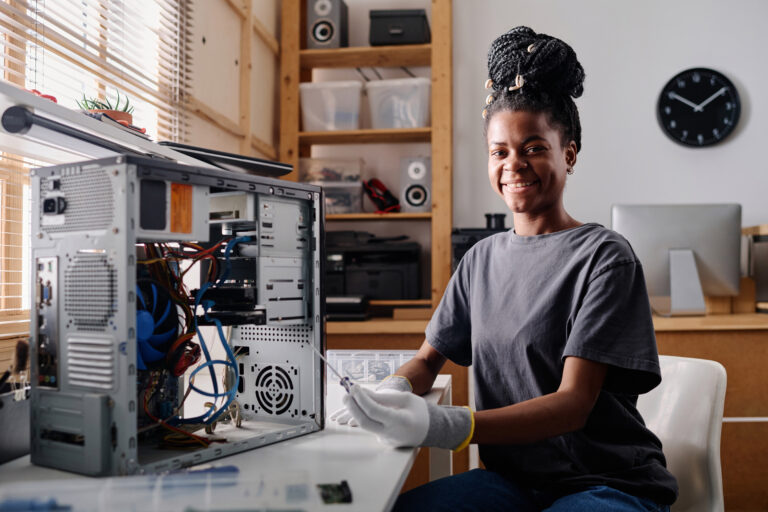
The cybersecurity industry is hungry for talent, yet breaking in can feel daunting. You might have a solid IT background

Gaia-X is a European initiative that aims to create a federated, secure, and transparent data infrastructure. Essentially, a “European cloud

In the 1980s, when payphones, modems, and bulletin board systems (BBSs) connected a secretive underground of digital explorers, one name




Articles you can enjoy without specific knowledge
Start learning new topics from their basic concepts
Get into the nitty-gritty of things with advanced topics
Crack your knuckles and get ready on your terminal