
Scam victimology: why did they pick me?
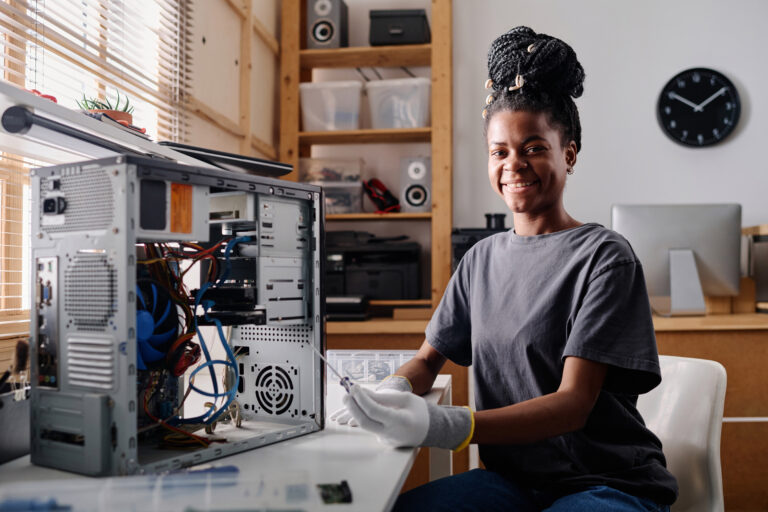
One of the most persistent myths about scams is that they only affect people who are inexperienced with technology or

One of the most persistent myths about scams is that they only affect people who are inexperienced with technology or
For decades, the security of modern cryptography has depended on the difficulty of mathematical problems. Factoring large numbers secures RSA.

It began as a simple video-sharing website in 2005. Since then, YouTube has grown into one of the most influential

Many people imagine scams as small, isolated crimes carried out by individuals sending suspicious emails from anonymous accounts. In reality,

For most of the twentieth century, strong cryptography was largely confined to governments, militaries, and a small group of specialists.

Every major technological shift has produced new conspiracy narratives. The printing press spread religious conspiracies. Radio amplified propaganda fears. The
Before the web, before social media, and even before most people had access to the Internet, there were bulletin board

Across the internet, identity has become increasingly flexible. People adopt avatars, usernames, and aesthetic personas that allow them to experiment

Fraud rarely announces itself. The first hints are subtle: an unusual email, a website discrepancy, or an irregular domain registration.




Articles you can enjoy without specific knowledge
Start learning new topics from their basic concepts
Get into the nitty-gritty of things with advanced topics
Crack your knuckles and get ready on your terminal