
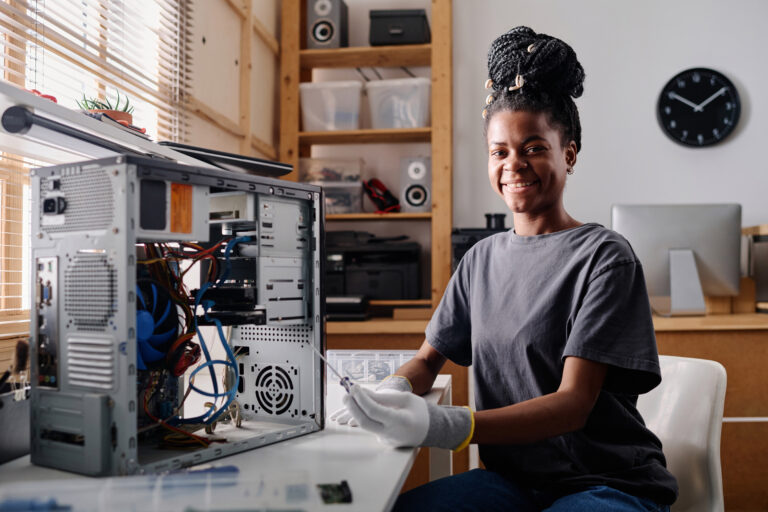
Women protecting digital privacy
Hacking is often framed as breaking in. But some of the most influential hackers have worked to protect systems, preserve

Hacking is often framed as breaking in. But some of the most influential hackers have worked to protect systems, preserve

For more than two decades, the cybersecurity community has relied on a shared language to identify security flaws in software

More and more websites, especially news sites and blogs, are showing cookie pop-ups that block access unless you click “accept

Spain’s cybersecurity framework reflects a hybrid model that combines centralized state security oversight with broad public–private coordination. As a country

How can organizations join or build a Gaia‑X AISBL-compliant environment? In this article, we will describe how to become a
Germany’s approach to cybersecurity is built on precision, structure, and accountability. As Europe’s largest economy and one of the EU’s
France is among the European countries with the most mature and well-structured cybersecurity ecosystems. Its government treats cybersecurity as a

In Canada, the Personal Information Protection and Electronic Documents Act, also known as PIPEDA, establishes the national standard for how

If 2013 marked the year Europe began to take cybersecurity seriously, the decade that followed transformed it into a legal




Articles you can enjoy without specific knowledge
Start learning new topics from their basic concepts
Get into the nitty-gritty of things with advanced topics
Crack your knuckles and get ready on your terminal