Computer-enabled crimes: virtual scams
Everybody knows what a scam is. But very few can recognize one when is directed at them. Why is that?
Everybody knows what a scam is. But very few can recognize one when is directed at them. Why is that?

When it comes to computer-enabled crimes, identity theft is only the first part of a deception scheme to fraud end

If Bonnie and Clyde had lived in our times, would they have still robbed a bank the way they did?
France is among the European countries with the most mature and well-structured cybersecurity ecosystems. Its government treats cybersecurity as a

Who invented Twitter? Long before Elon Musk came into the picture, the architect of Twitter was a quiet figure from

On October 28, 2017, an anonymous poster calling themself “Q Clearance Patriot” made a short, cryptic post on 4chan. Over

In July 2017, one of the most ambitious global cyber operations ever executed quietly brought down the largest illegal marketplace

Gaia-X is a European initiative that aims to create a federated, secure, and transparent data infrastructure. Essentially, a “European cloud

In the 1980s, when payphones, modems, and bulletin board systems (BBSs) connected a secretive underground of digital explorers, one name


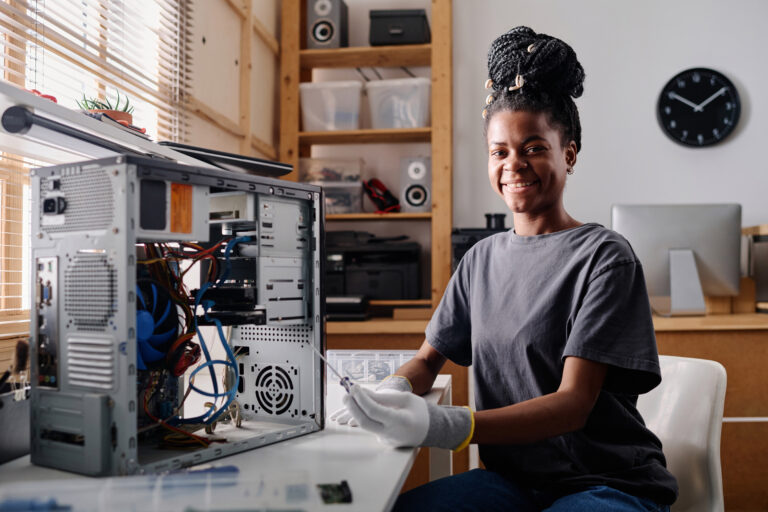


Articles you can enjoy without specific knowledge
Start learning new topics from their basic concepts
Get into the nitty-gritty of things with advanced topics
Crack your knuckles and get ready on your terminal