
HUMINT: the art of getting human intel
Human Intelligence (HUMINT) is the practice of gathering information from people rather than systems. While OSINT and SOCMINT focus on

Human Intelligence (HUMINT) is the practice of gathering information from people rather than systems. While OSINT and SOCMINT focus on

The Internet has layers, some visible to everyone and others less obvious, often referred to as the hidden web (deep

Social media platforms provide a continuous stream of human behaviour, identity construction, and interaction. For investigators, social media profiling is

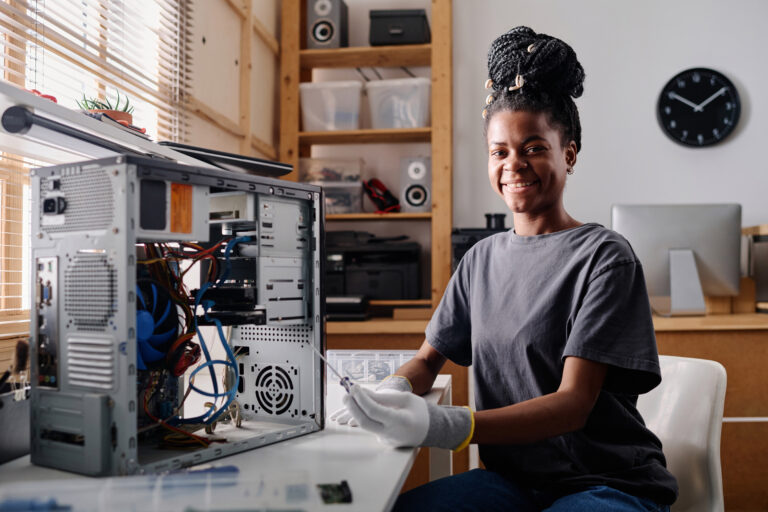
If hardware gives robots their bodies, artificial intelligence gives them their behaviour. AI is a game changer for robotics: without
Some websites are purposely built as Internet experiments: temporary spaces where ideas are tested, behaviours are observed, and new forms

Artificial intelligence has already reshaped industries, workflows, and daily life. Yet, what we see today is still an early stage

Quantum computing is no longer an exclusive domain of physicists. Developers now have access to frameworks, simulators, and cloud-based quantum

Constant connectivity has become the default state of modern life. Notifications, messages, updates, and content streams create an environment where

The history of cryptography is often told through the names of mathematicians, wartime code-breakers, and modern computer scientists whose work




Articles you can enjoy without specific knowledge
Start learning new topics from their basic concepts
Get into the nitty-gritty of things with advanced topics
Crack your knuckles and get ready on your terminal