
Paul Mockapetris and DNS
In the early days of the Internet, computers were identified solely by numerical addresses. While machines handled these identifiers easily,

In the early days of the Internet, computers were identified solely by numerical addresses. While machines handled these identifiers easily,

More and more websites, especially news sites and blogs, are showing cookie pop-ups that block access unless you click “accept

Spain’s cybersecurity framework reflects a hybrid model that combines centralized state security oversight with broad public–private coordination. As a country

As the year comes to a close, many people are thinking about what to carry into 2026 and what to

2025 has been a year often dominated by headlines about risk, disruption, and AI overhype. However, this year also delivered

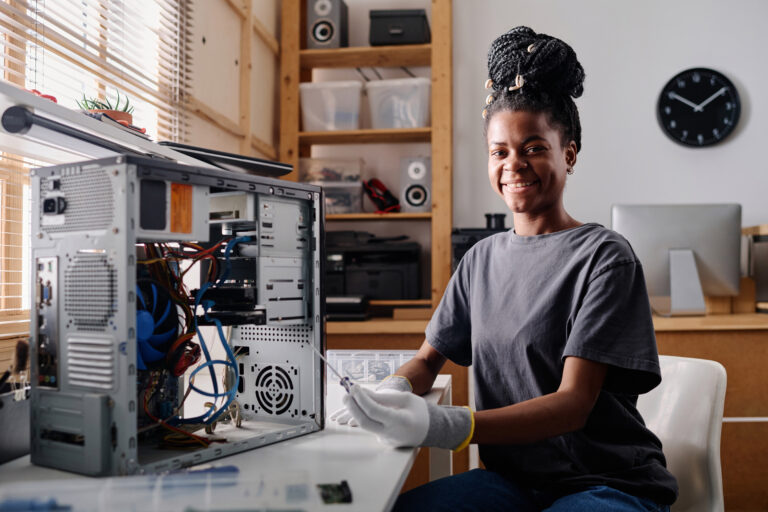
When most people think about online security, they picture complex tools or advanced technical training. Tejasvi Manoj, named TIME’s Kid

If you google famous real life hackers, you will come up with names like Kevin Mitnick, Albert Gonzales, Adrian Lamo.

Let’s explore a few playful myths from digital life. Many of these stories float around social media or get shared

Offensive security roles attract people who enjoy thinking creatively, solving puzzles, and understanding systems from the inside out. Whether you




Articles you can enjoy without specific knowledge
Start learning new topics from their basic concepts
Get into the nitty-gritty of things with advanced topics
Crack your knuckles and get ready on your terminal