The SolarWinds Supply Chain Attack
Imagine downloading a patch to update a critical system, and that patch contained the malware to hack you. That really
Imagine downloading a patch to update a critical system, and that patch contained the malware to hack you. That really

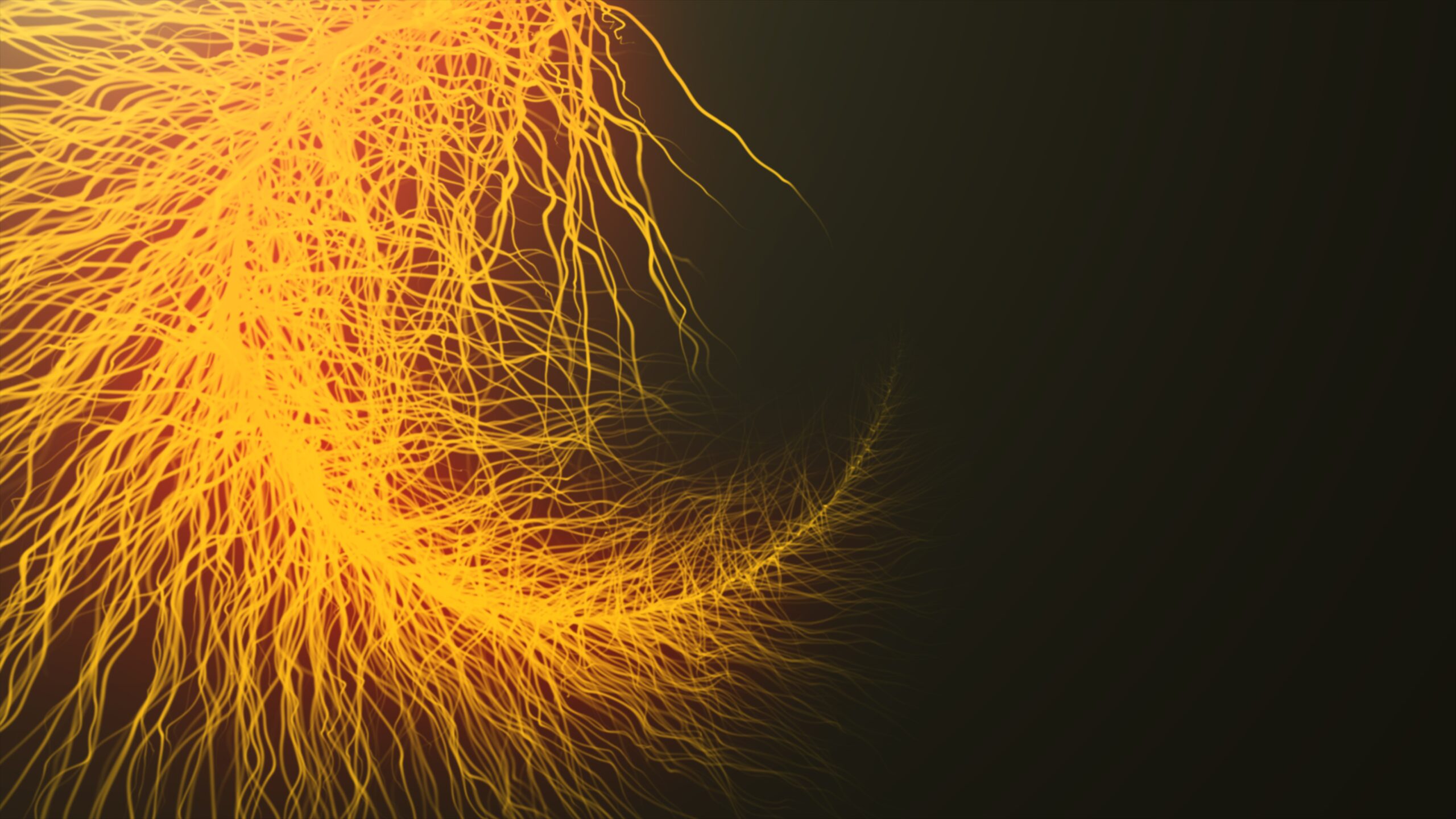
If you work in cybersecurity in a technical capacity, you probably operate with a few different operating systems. And while

Have you ever lost access to your WordPress website? Instead of wasting hours with your hosting provider trying to explain

In one of our previous articles, we introduced you to SSH authentication and its basic usage. However, you can’t use

In May 2013, a group of journalists at The Guardian started receiving classified information through encrypted channels from an anonymous

How do you access a computer without physically having access to it? How can you execute commands from another computer?

Unix is a powerful, multiuser operating system that serves as the foundation for Linux and MacOS. The Unix command-line interface

If you work as a contractor for the United States Government, you must comply with stricter security rules than standard

Many people entering the cybersecurity field believe that the only way to demonstrate their skills to a prospective employer is




Articles you can enjoy without specific knowledge
Start learning new topics from their basic concepts
Get into the nitty-gritty of things with advanced topics
Crack your knuckles and get ready on your terminal