For decades, the security of modern cryptography has depended on the difficulty of mathematical problems. Factoring large numbers secures RSA. Discrete logarithms underpin Diffie–Hellman key exchange. Elliptic curve cryptography relies on the hardness of solving equations over finite fields. Classical computers make these tasks infeasible at the scales used in practice, and that is the foundation of digital trust.
But a new threat is emerging. Quantum computing promises to solve some of these problems exponentially faster than classical machines. The cryptographic assumptions that protect our online communications, financial transactions, and digital identities may no longer hold. Post-quantum cryptography is the field dedicated to preparing for this possibility.
Why quantum computing could change everything
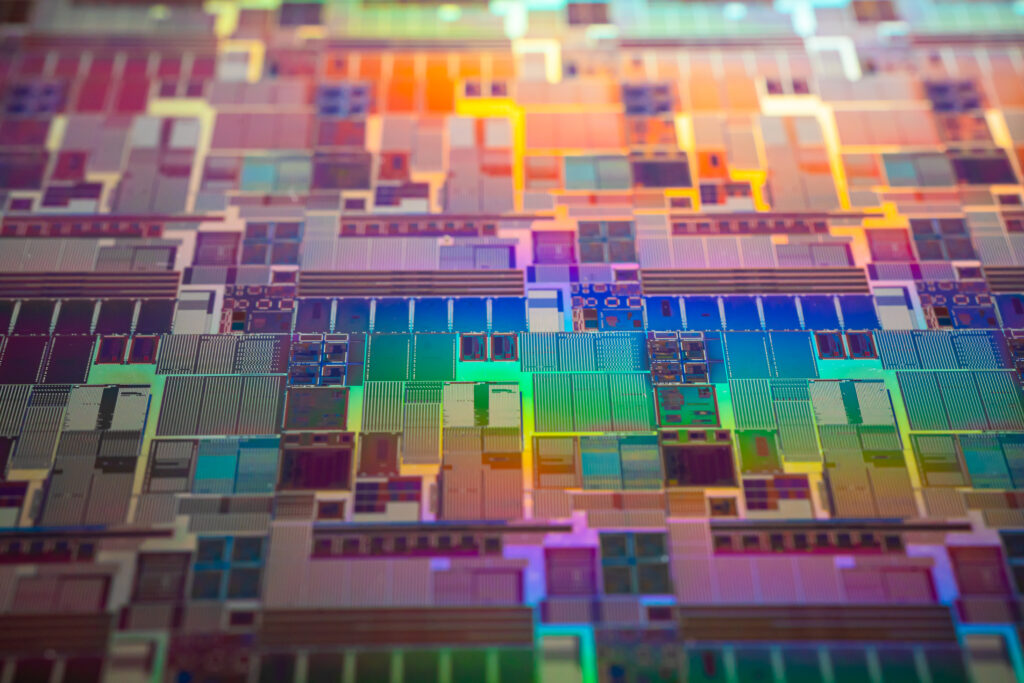
Quantum computers operate on fundamentally different principles than classical computers. Instead of bits, they use quantum bits, or qubits, which can exist in multiple states simultaneously due to superposition. They can also exploit entanglement, a phenomenon that allows correlated qubits to affect each other instantaneously over distance.
This enables certain algorithms to outperform classical ones dramatically. For example, Shor’s algorithm can factor large integers in polynomial time. An RSA key that would require thousands of years to break on a conventional computer could theoretically be broken in hours or minutes on a sufficiently powerful quantum machine. Similarly, Grover’s algorithm can accelerate brute-force search of symmetric keys, effectively halving the effective key length.
While large-scale, fault-tolerant quantum computers are still under development, the potential threat is real enough that governments, corporations, and cryptographers are preparing now.
The principles of post-quantum cryptography
Post-quantum cryptography (PQC) does not rely on quantum computing itself. Instead, it seeks algorithms that remain secure even against quantum attacks. The goal is to replace vulnerable primitives (like RSA and ECC) with alternatives that quantum algorithms cannot easily compromise.
Current PQC approaches include:
- Lattice-based cryptography builds security on the difficulty of solving high-dimensional lattice problems. Examples: NTRU, Kyber.
- Code-based cryptography uses error-correcting codes, where decoding random linear codes is hard. Example: McEliece.
- Multivariate polynomial cryptography relies on solving systems of nonlinear equations over finite fields.
- Hash-based signatures uses only secure hash functions to create signatures resistant to quantum attacks.
These methods are designed to withstand both classical and quantum adversaries while remaining efficient enough for practical use.
The challenges
Transitioning to post-quantum cryptography is not as simple as swapping out one algorithm for another. Digital infrastructure is vast, and cryptography is deeply embedded in software, hardware, and communication protocols.
To coordinate this transition, the National Institute of Standards and Technology (NIST) has been running a multi-year process to evaluate and standardize post-quantum cryptographic algorithms. The selected candidates must balance security, performance, and ease of integration.
Even after standards are finalized, implementation poses challenges:
- Key and signature size: some PQC algorithms require larger keys or signatures, impacting storage, bandwidth, and system performance.
- Hybrid approaches: many systems initially combine classical and post-quantum algorithms to maintain security during the transition.
- Legacy systems: older devices and software may be difficult or impossible to upgrade, creating uneven adoption.
The complexity of this transition highlights that cryptography is not just mathematics; it is infrastructure.
Harvest now, decrypt later
A critical concern is the concept of “harvest now, decrypt later.” Adversaries may record encrypted communications today with the hope of decrypting them once quantum computers become capable. This is particularly relevant for sensitive long-term data such as government documents, medical records, or financial information.
Post-quantum cryptography aims to prevent this scenario. Even if encrypted data is intercepted and stored now, the future use of quantum computers should not allow retroactive decryption.
Add Your Heading Text Here
The advent of quantum computing does not render current cryptography immediately obsolete. For most applications, existing protocols remain secure for now. But the timeline for practical quantum machines is uncertain, and the consequences of underestimating the threat are severe.
Post-quantum cryptography represents proactive preparation. It acknowledges that cryptographic assumptions are contingent on technology. By designing algorithms that remain secure under new paradigms, we preserve trust in digital communication for decades to come.
The ongoing work in PQC is an extension of the historical pattern: as computational power and networks evolve, cryptography adapts. What was secure yesterday may be vulnerable tomorrow, and protecting confidentiality, integrity, and authenticity requires constant vigilance.